Claude Security: How Anthropic's AI Code Scanner Works, What It Finds, and How It Compares to Snyk and SonarQube (2026)
AI is compressing the timeline between vulnerability discovery and exploitation. That is the sentence Anthropic used to open the Claude Security public beta announcement on April 30, 2026. It's not marketing language. It's a factual description of what is happening right now.
Claude Mythos Preview — Anthropic's most restricted model, available only to vetted partners — can match or surpass elite human security researchers at both finding and exploiting software vulnerabilities. That capability will become more broadly available within a year or two. When it does, attackers will use it.
Claude Security is Anthropic's answer for the wider enterprise market. Powered by Claude Opus 4.7 and accessible today at claude.ai/security for all Claude Enterprise customers, it puts the defensive side of that capability in front of security teams before attackers get the offensive side. No API integration. No custom agent build. Just point it at a GitHub repository and start scanning.
In the two months since the closed research preview launched in February, teams have already discovered 500+ vulnerabilities that survived years of expert review and conventional scanning. Here's everything you need to know — including what it actually does, how it compares to the tools you're already running, and what the honest limitations are.
The Problem Claude Security Is Solving
Traditional code security scanners have a false positive problem that is quietly destroying the value of the tools themselves. Multiple industry studies put SAST tool false positive rates between 30% and 70%. At the high end, that means seven out of ten alerts your team investigates are dead ends.
The math on wasted capacity is stark. A 5-person security team spending 40% of their time triaging non-exploitable findings is losing two full-time engineers' worth of productivity. At a loaded cost of $150,000 per engineer per year, that's $300,000 annually in wasted security capacity — before you account for what they're not doing instead.
Worse than the cost is the behavioral response: alert fatigue. When developers learn that most SAST findings are false positives, they stop investigating. Actual vulnerabilities get ignored because they look like every other false alarm in the queue. Security teams receive an average of 4,484 alerts per day and spend up to 27% of their time on findings that turn out to be non-exploitable.
The root cause is architectural. Traditional SAST tools are pattern matchers. They search for code patterns that resemble known vulnerability signatures. This approach has a fundamental ceiling: it cannot understand context. A tool may flag a variable as 'user input reaching a SQL query' without knowing that a sanitizer was applied in between. It may fire on hardcoded passwords in test constants, example strings, or documentation. It may not recognize that ASP.NET Core's built-in SQL parameterization already handles the case it's flagging.
There is also a new pressure that did not exist two years ago. According to a 2026 study on 534 code samples from six LLMs, 25.1% of AI-generated code snippets contain confirmed security flaws. With 72% of organizations now using AI for code generation, the volume of code being produced has exploded — and a meaningful fraction of it has security issues baked in from generation. For a deeper look at how Claude handles code quality and safety decisions, the Claude Code Auto Mode guide covers how Claude's safety classifier catches risky actions before they execute.
Claude Security is designed to attack the false positive problem at the architectural level, not just tune the parameters.
How Claude Security Works (Step-by-Step)
Claude Security does not search for known vulnerability patterns. It reads and reasons about code the way a human security researcher does — which is a genuinely different approach, not a marketing reframe of the same underlying technology.
Here is what happens during a scan:
Step 1: Select your repository and scope
Access Claude Security from the Claude.ai sidebar or directly at claude.ai/security. Select one of your GitHub repositories. You can target the full repository, a specific directory, or a specific branch. This scoping is especially useful for scanning recently changed code or a particular microservice before a release.
Step 2: Claude reads and reasons across files
Rather than running pattern matches against each file in isolation, Claude reads source code across files and modules, traces how data moves through the application, and examines how components interact. The model follows execution paths, tracks variable propagation, and observes how dependencies affect the security posture of the overall system.
This is where the LLM reasoning advantage shows up most clearly. A classic SQL injection requires tracing: where does user input enter the system, what transformations happen to it, and where does it reach the database query. That chain may cross four different files and two abstraction layers. Rule-based scanners need explicit rules for each path. Claude understands the semantic meaning of the code and can follow the chain even in novel patterns it was not explicitly trained to recognize.
Step 3: Multi-stage validation pipeline
Before surfacing any finding to an analyst, Claude runs each potential vulnerability through its own internal validation. The model challenges its own conclusions: is the data flow actually reachable? Is the sink actually exploitable given the framework's default behavior? Is there sanitization happening somewhere in the call chain that the initial analysis missed?
Quotable: "Claude Security uses a multi-stage validation pipeline where Claude challenges its own findings before surfacing them to an analyst, reducing false positives and attaching a confidence rating to every result." — Anthropic, April 30, 2026
Step 4: Structured findings with confidence ratings
Each validated finding includes: a confidence score (how certain Claude is that this is a real, exploitable issue), a severity rating (High/Medium/Low based on exploitability in your specific codebase, not just the vulnerability category), a detailed explanation of the likely impact, reproduction steps that would trigger the vulnerability, and a suggested patch.
The confidence score is the practical mechanism for eliminating alert fatigue. High-confidence findings are what security teams should act on immediately. Medium-confidence findings warrant review. Low-confidence findings provide coverage without demanding immediate triage.
Step 5: Fix in Claude Code
When a finding is ready to fix, users can open Claude Code directly in the context of the affected repository and work through the patch there. The full Claude AI 2026 guide covers how Claude Code's agentic loop operates — Claude Security feeds directly into that same surface for remediation, so the time from scan to applied patch can happen in a single sitting rather than the days-long back-and-forth between security and engineering teams that teams reported before.
What's New in the Public Beta vs the February Research Preview
The February 2026 research preview of Claude Code Security showed proof of concept. Hundreds of organizations got access, found real vulnerabilities, and gave Anthropic detailed feedback on what enterprise security teams actually need in production. The April 30 public beta reflects that feedback directly.
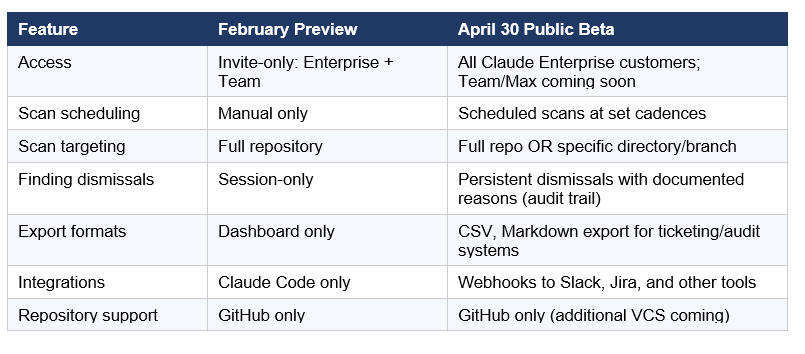
The scheduled scans addition is the most operationally significant. Enterprise security teams do not want to run one-off audits — they want continuous coverage. Setting a weekly or monthly scan cadence and receiving results automatically transforms Claude Security from a diagnostic tool into a monitoring layer.
The persistent dismissals with documented reasons are the second significant addition. In security workflows, documented triage decisions matter for compliance. When a future auditor asks why a finding was dismissed, 'we decided it was acceptable because the data never reaches an external sink in our architecture' needs to be on record — not just known to whoever clicked the button.
For context on how Claude's model capabilities evolved between the February preview (Claude Opus 4.6) and this beta (Claude Opus 4.7), the April 2026 AI models benchmark comparison covers the specific security and coding improvements in Opus 4.7
Claude Security vs Snyk vs SonarQube vs GitHub Advanced Security
These are not competing tools doing the same thing. They have fundamentally different architectures, different strengths, and in most mature enterprise security setups, they are complementary rather than mutually exclusive. Understanding where each wins is more useful than a simple ranking.
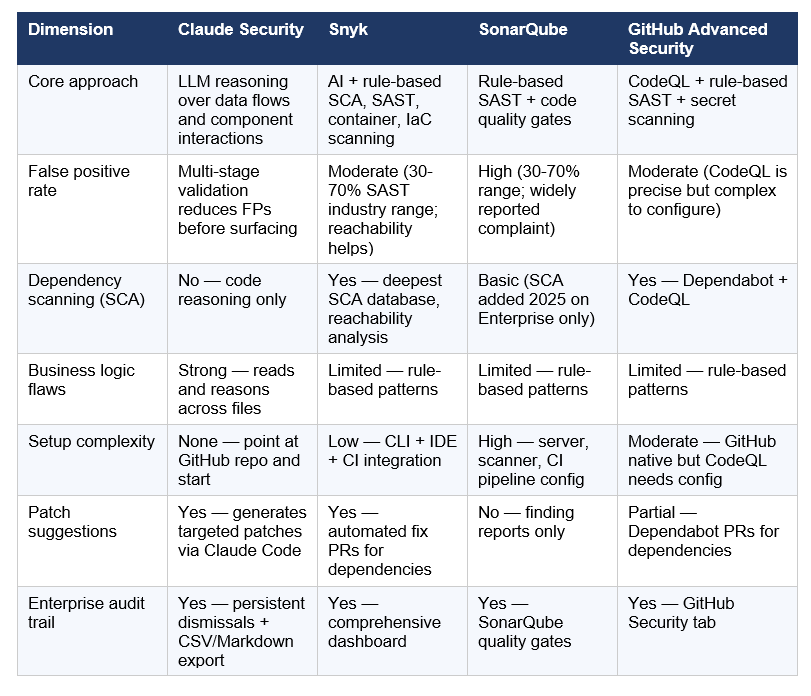
The honest framing: Claude Security does something different from what Snyk and SonarQube do. It reasons semantically about business logic flaws, novel data flow vulnerabilities, and complex multi-file interactions that pattern-based tools miss by design. Snyk's strength is dependency vulnerability coverage — its SCA database and reachability analysis are industry-leading for catching CVEs in your open-source packages. SonarQube's strength is code quality enforcement and compliance reporting across large codebases.
My take: most mature enterprise security stacks will run Claude Security alongside Snyk, not instead of it. Use Snyk for dependency CVEs and container scanning. Use SonarQube if you need code quality gates for engineering leadership. Use Claude Security for the business logic flaws, novel vulnerability classes, and complex multi-component issues that neither of the other two tools will catch. The February preview finding 500+ vulnerabilities that had survived years of expert review and Snyk scanning makes that case better than any benchmark.
For readers evaluating coding tools that overlap with security, including how Cursor's same-day Security Review response works, the Cursor Composer 2 benchmarks and review covers the competing agentic coding and security landscape.
The Partner Ecosystem: CrowdStrike, Palo Alto, Wiz, and More
Claude Security is not just a standalone product — it's the consumer-facing surface of a much larger Anthropic cybersecurity strategy announced simultaneously on April 30, 2026.
On the technology partner side, six major security platforms announced they are integrating Claude Opus 4.7 directly into their existing products:
- CrowdStrike — Opus 4.7 integrated across the CrowdStrike Falcon platform (announced as Project QuiltWorks). CrowdStrike is part of Anthropic's Cyber Verification Program.
- Microsoft Security — Opus 4.7 integration for security workflows across the Microsoft security platform.
- Palo Alto Networks — Embedding Opus 4.7 for AI-powered vulnerability discovery and remediation.
- SentinelOne — Opus 4.7 integration for enterprise defense.
- TrendAI — Trend Micro's AI security platform integrating Claude's reasoning capabilities.
- Wiz — Cloud security platform adding Opus 4.7 for vulnerability detection in cloud environments.
On the services side, Accenture, BCG, Deloitte, Infosys, and PwC are all now helping organizations deploy Claude-integrated security solutions for vulnerability management, secure code review, and incident response programs.
This partner ecosystem matters because it answers the most likely enterprise objection: 'We already have CrowdStrike. Why do we need Claude Security separately?' The answer is that you may not need to adopt it separately — Opus 4.7's reasoning capabilities are coming to the security platforms enterprises already run. The three access paths are: directly in Claude Security at claude.ai/security, embedded in a platform you trust, or with a services partner guiding the rollout.
For context on where Claude Opus 4.7 sits in the broader AI model landscape compared to GPT-5.5 and Gemini 3.1 Pro — the models powering competing security tools — the full AI models leaderboard and comparison covers the benchmarks in detail.
Honest Limitations: What Claude Security Can't Do Yet
I want to be straight about what is not in the public beta, because the launch coverage is mostly positive and that means the gaps need to be stated clearly.
- GitHub only: Claude Security currently supports only GitHub-hosted repositories. Teams on GitLab, Bitbucket, Azure DevOps, or self-hosted Git will need to wait for additional VCS support, which Anthropic has not announced a timeline for.
- No dependency scanning (SCA): Claude Security scans the code you write, not the packages your code depends on. If you need to detect known CVEs in your npm, PyPI, or Maven dependencies, you still need Snyk or GitHub Dependabot. Claude Security and Snyk are not alternatives in this dimension — they're addressing different attack surfaces.
- Enterprise only (for now): The public beta is limited to Claude Enterprise customers. Claude Team and Max plan access is coming soon, but no date has been announced. Individual developers and small teams with Pro plans cannot access this today.
- Cyber safeguards may interrupt legitimate work: Opus 4.7 includes built-in cyber safeguards designed to block prohibited requests. Organizations whose legitimate security work triggers these safeguards — red teams, penetration testers, security researchers doing exploit development — can apply to Anthropic's Cyber Verification Program to continue operating without interruption.
- No DAST, container, or IaC scanning: Claude Security scans source code. It does not scan running applications (DAST), container images, or infrastructure-as-code configurations. For full-stack coverage, it needs to be complemented with tools that address those surfaces.
For readers who want to understand the broader security landscape around Claude Code, including the March 2026 source code exposure incident, the full Claude Code source code leak analysis covers what was exposed and what it revealed about Anthropic's internal security architecture.
Who Should Use Claude Security — and Who Should Wait
The decision is simpler than most coverage is making it.
Use Claude Security now if:
- You're a Claude Enterprise customer with GitHub-hosted repos — access is immediate with no setup required.
- Your codebase has significant AI-generated code. The 25.1% vulnerability rate in AI-generated code is precisely the class of issue that pattern-based scanners miss and Claude Security is designed to catch.
- Your security team is drowning in false positive alerts from existing SAST tools. Claude Security's multi-stage validation and confidence scoring are designed specifically for this problem.
- You've experienced the 'scan to fix in days' problem that Anthropic's early users described — the back-and-forth between security and engineering teams. The direct Claude Code integration closes that loop.
Wait if:
- You're not on Claude Enterprise yet. Team and Max plan support is coming — but not today.
- Your primary security gap is dependency vulnerabilities in open-source packages. That's Snyk's territory, and Claude Security doesn't address it.
- Your repositories are on GitLab, Bitbucket, or Azure DevOps. GitHub is the only supported integration right now.
- You need full-stack coverage including DAST, container scanning, or IaC analysis. You'll still need Snyk, Wiz, or Checkmarx for those surfaces.
If you want to start building security reasoning workflows using Claude's API while waiting for plan availability, the Build Fast with AI agent-building notebooks include implementation patterns for Claude-powered code analysis and orchestration workflows.
Frequently Asked Questions
What is Claude Security?
Claude Security is an AI-powered code vulnerability scanner launched in public beta on April 30, 2026, by Anthropic. It uses Claude Opus 4.7 to scan GitHub repositories, trace data flows across files and modules, identify security vulnerabilities through reasoning (not pattern matching), and generate targeted patch suggestions. It is available to Claude Enterprise customers at claude.ai/security with no API integration or custom agent build required.
How is Claude Security different from traditional SAST tools like SonarQube?
Traditional SAST tools like SonarQube use rule-based pattern matching — they flag code that matches known vulnerability signatures. This produces false positive rates of 30-70% because the tools cannot understand context (they don't know if sanitization was applied, or if a framework handles the case automatically). Claude Security reads and reasons about code like a human security researcher: it traces data flows, understands component interactions, and verifies findings through a multi-stage validation pipeline before surfacing them. It attaches a confidence score to every finding, so teams know which alerts are worth acting on immediately.
What types of vulnerabilities does Claude Security detect?
Claude Security is designed for complex, context-dependent vulnerabilities that pattern-based scanners miss: business logic flaws, broken access control, injection risks that span multiple files, unsafe data flows across modules, authentication and authorization issues, exposed secrets in non-obvious locations, and logic flaws that require understanding how components interact. In the February 2026 research preview, it found over 500 previously undetected vulnerabilities in production open-source codebases, including bugs that had survived years of expert review and conventional scanning.
Does Claude Security replace Snyk?
No — they address different attack surfaces and are complementary. Snyk's primary strength is software composition analysis (SCA): detecting known CVEs in your open-source dependencies using a comprehensive vulnerability database with reachability analysis. Claude Security scans the code you write for novel and complex vulnerabilities that rule-based tools miss. Most mature enterprise security teams will run both: Snyk for dependency CVEs and container scanning, Claude Security for business logic and complex data flow vulnerabilities.
Is Claude Security available for individual developers or small teams?
As of April 30, 2026, Claude Security is in public beta exclusively for Claude Enterprise customers. Support for Claude Team and Max plan customers is coming soon, but Anthropic has not announced a specific date. Individual developers and Pro plan users cannot access Claude Security yet. Anthropic has encouraged open-source maintainers to apply for expedited access through a separate program.
What is a confidence score in Claude Security?
A confidence score is Claude's assessment of how certain it is that a reported finding represents a real, exploitable vulnerability in your specific codebase. Before surfacing any finding to an analyst, Claude runs a multi-stage validation where it challenges its own conclusions — checking whether the data flow is actually reachable, whether sanitization might be applied further down the call chain, and whether the framework's default behavior handles the case. The confidence score reflects the result of that validation. High-confidence findings should be triaged immediately; lower-confidence findings provide coverage without demanding urgent response.
How do I access Claude Security?
Claude Security is accessible in two ways for Claude Enterprise customers: through the Claude.ai sidebar (look for the Security option) or directly at claude.ai/security. From there, you select a GitHub repository or scope to a specific directory or branch, then start a scan. No additional API configuration, custom agent build, or infrastructure setup is required. Findings appear in a dashboard with severity ratings, confidence scores, impact explanations, and patch suggestions.
What is the relationship between Claude Security and Project Glasswing?
They are separate initiatives at different capability and access levels. Project Glasswing is Anthropic's restricted program that makes Claude Mythos Preview — its most powerful security model, capable of matching elite human security researchers at both finding and exploiting vulnerabilities — available to a small number of vetted partners. Claude Security is the broader enterprise product, powered by the generally available Claude Opus 4.7, designed for organizations that want to scan their codebases defensively without needing the restricted Mythos access. Claude Security is the 'on-ramp' for the wider enterprise market; Project Glasswing is the frontier capability for specialized partners.
Recommended Blogs
Related reading from Build Fast with AI:
- Claude AI 2026: Complete Models, Features & What's Coming Guide
- Claude Code Auto Mode: Unlock Safer, Faster AI Coding (2026 Guide)
- Claude Code Source Code Leak: The Full Story 2026
- 150 Best Claude Prompts That Work in 2026 (Including Security Audit Prompts)
- Best AI Models April 2026: GPT-5.5, Claude & Gemini Compared
- Cursor Composer 2: Benchmarks, Pricing & Review (2026)
- Best AI for Coding 2026: Nemotron vs GPT-5.3 vs Opus 4.6
References
- Anthropic — Claude Security Is Now in Public Beta (Official Announcement, April 30, 2026)
- Anthropic — Claude Code Security Limited Research Preview Launch (February 20, 2026)
- SecurityWeek — Anthropic Unveils Claude Security to Counter AI-Powered Exploit Surge
- SiliconANGLE — Anthropic Announces Claude Security Public Beta to Find and Fix Software Vulnerabilities
- The New Stack — Anthropic's Claude Security Emerges from Closed Preview
- Cyber Kendra — Anthropic's Claude Security Is Now Open to All Enterprise Users
- CrowdStrike — Puts Claude Opus 4.7 to Work Across the Falcon Platform (Project QuiltWorks)
- Snyk — Claude Code Security: A Welcome Evolution in the Remediation Loop
- Offensive360 — AI-Powered SAST: The Future of Code Security in 2026
- Practical DevSecOps — AI Security Statistics 2026: Latest Data and Research
- Build Fast with AI — gen-ai-experiments: Agent-Building Notebooks for Claude-Powered Workflows